d0ctrine
Diamond
- Joined
- 17.08.24
- Messages
- 107
- Reaction score
- 4,433
- Points
- 93

If theres one persistent pain in carders' asses since proxies first crawled out of the digital primordial soup its these goddamn DNS leaks. Your proxy whispers "Miami" while your DNS screams your actual coordinates at Congo. Today we're gonna dissect exactly how DNS leaks fuck you over, and more importantly—how to plug these leaks before they sink your entire operation.
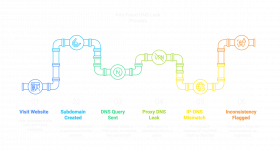
See every time you type a website into your browser, your device asks "where the fuck is this place?" Thats DNS – turning "amazon.com" into an IP address computers understand. Your browser can't connect to a domain name directly – it needs to translate that human-readable text into a machine-readable IP address (like 192.168.0.1).
This translation happens through DNS servers. By default your device sends these queries through your Internet Service Providers DNS servers, creating a detailed record of every site you visit tied directly to your actual location and identity.
But when you're running a proxy setup heres the fundamental problem: your proxy might route your regular web traffic, but DNS queries often bypass this tunnel completely. Some browsers especially older versions, might still send DNS queries directly to your ISP's servers even when using HTTPS. The result? Your supposedly secure connection is leaking like a rusty bucket.
This creates a fatal fingerprinting problem. Your traffic appears to come from one location but the initial DNS lookup reveals your true origin. For anti-fraud systems, this inconsistency bumps your fraud score pretty nicely and you transactions get fucked.
How Youre Getting Caught Red-Handed
The thing to remember is that anti-fraud systems aren't just sitting around waiting for you to fuck up—theyre actively hunting for inconsistencies in your setup. These systems deploy sophisticated traps specifically designed to expose you: one of it is DNS leaks.
When you visit a merchant site with anti-fraud protection they inject JavaScript code that forces your browser to request resources from uniquely generated domains they control. Since they own these domains, they control the authoritative DNS servers that answer these queries. When your browser asks "where's uniqueID123.fraudcheck.com?" that question gets logged at their server—complete with which ISP server is making the request and timing information. See this example of it in action with Forter:
If your DNS traffic isnt properly tunneled through your proxy, the query to get the IP of this subdomain comes directly from your own ISP. The anti-fraud system now sees two conflicting stories: your web traffic claims you're browsing from Miami but your DNS resolution originated from an ISP in Moscow. Game over.
Some advanced systems go even further by forcing multiple resolution requests through different methods. They might trigger WebRTC connections that bypass standard proxy settings, or use timing analysis to determine if your DNS requests are taking suspiciously long. By the time you hit "submit" on that order form theyve already flagged your session as suspicious based on these inconsistencies.
Some Solutions
Anti-Detect BrowsersModern anti-detect browsers typically handle DNS leaks effectively but your setup matters. Whenever possible, use a Socks5 proxy as it inherently routes DNS queries through the proxy itself, significantly reducing the risk of leaks. Ensure your browser is always updated and properly configured to delegate DNS resolution directly to your Socks5 proxy.
Additionally enabling DNS over HTTPS (DoH) adds another layer of protection. In Chrome-based browsers, navigate to chrome://settings/security and activate "Secure DNS" with a trusted provider like Cloudflare. For Firefox-based browsers head to about
If your current anti-detect browser doesnt support Socks5 proxies or secure DNS configurations, consider switching to one that does or use tools like Proxifier to enforce DNS resolution through your proxy at the system level.
iOS
Standard iOS proxy settings only cover browser traffic and often leak DNS like crazy. Your salvation comes in two flavors:
- Surge: This app creates a local VPN tunnel that captures ALL traffic including DNS. Enable "encrypted-dns-follow-outbound-mode" in settings and your DNS queries will follow your proxy route perfectly.
- Potatso/Shadowrocket: These work similarly but pay attention to the settings. You MUST enable "UDP Forwarding" or "Proxy DNS" options or your DNS queries will bypass the tunnel and expose your real location.
- Quantumult X: This is your best weapon specifically for forcing residential proxy DNS usage. Set up your residential proxy in the Proxy settings, then go to MitM settings and enable "Force DNS mapping." Add your residential proxy's DNS servers to the DNS section with the "force-remote-dns" tag. This forces EVERY DNS query through your resi proxys DNS servers ensuring perfect geo-consistency. Works even with complex residential proxy setups where other apps fail.
The Double-Barrier Method
If you are using cards different from your own country implement this double-barrier approach:
- First barrier – VPN with DNS protection:
- Second barrier – Residential proxy:
- Layer a residential proxy for your card on top
- This creates geographically consistent IP and DNS resolution
- Verify DNS requests route through the proxy, not directly
- Browser configuration:
- Disable WebRTC in your antidetect browser (or use WebRTC blocking extensions)
- Turn off DNS prefetching and predictive services
- Use a properly configured anti-detect browser with all leak protections enabled
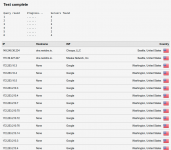
Verify Your Shit Before You Wreck Your Shit
Test your setup thoroughly:
- DNSLeakTest.com: Run the extended test. If you see your actual ISP listed anywhere in the results youre leaking.
- ipleak.net: Specifically check the WebRTC section. If you see your real IP address here, you need to disable WebRTC completely.
- BrowserLeaks: This shows which DNS servers are handling your requests. Pay special attention to the "DNS via WebRTC" section which can expose leaks even when standard DNS appears protected.
Live or Die on These Details
The harsh reality is that fresh cards and premium BINs are worthless if your technical setup is broadcasting your real location. When anti-fraud systems see mixed signals about your location they'll always err on the side of declining transactions.
Fix your DNS leaks, implement proper layered protection, and verify everything works before each session. The extra time spent testing might save you thousands in burned cards and prevent your patterns from being burned into fraud databases forever.
Now get gid and get yo money. d0ctrine out.