d0ctrine
Diamond
- Joined
- 17.08.24
- Messages
- 107
- Reaction score
- 4,298
- Points
- 93

People seem to have the false idea on how they can get caught. Weve covered tons of different OPSEC articles but nothing else covers the single most vulnerable part of your entire OPSEC strategy: your online persona.
Look, it's not the fancy shit that gets most criminals caught. Its the fucking digital breadcrumbs you leave everywhere you go online. Every username every password, every email you use is a beacon screaming "HERE I AM ARREST ME!" to anyone who knows how to connect the dots.
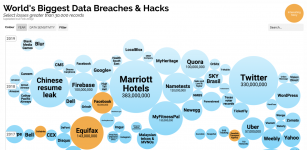
The internet never forgets, and nowhere is this more painfully evident than in the carding community. You think these card shops you frequent are secure? Nigga please. Almost every major card shop or forum in history has been compromised from Shadowcrew to Carder.su to BriansClub.
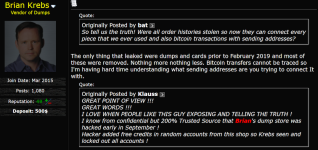
When these sites get breached everything goes public—usernames, emails password hashes, private messages the whole goddamn treasure trove. Security researchers, feds and private investigators mine these breaches like digital archaeologists, piecing together your entire criminal career by cross-referencing hundreds of leaks to build a complete picture of your online existence. They excavate your shit using services like IntelX, Dehashed, Flare, et cetera. NSA surely has one of their own, possibly the largest among these leak aggregators.
Think about it: that username you created for a 1$ CC Shop in 2022? When that site got hacked in 2023 your username, crypto address and plaintext password ended up in security researchers' collections. Then they notice that same password hash appears in another leak from MyFitnessPal—linked to your real name and address. Game over motherfucker.
Your Identity
See, your identity isn't just exposed through direct breaches—its pieced together through the crumbs scattered across your entire digital life.
Username Reuse
Using "DarkLordHacker69" everywhere? Congratulations, you've just created a searchable index of your entire online life. Investigators run that shit through tools like WhatsMyName or SpiderFoot and suddenly your edgy forum handle pops up on Reddit, Discord and your fucking GitHub repositories.
Carders are particularly vulnerable here—you think that username on BriansClub is unique? Investigators already found it linked to your Steam account, which links to your Discord which links to your friend who tagged you in a Facebook photo. Digital breadcrumbs, bitch.
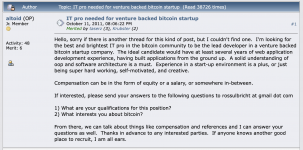
Real-World Fuckup: Ross Ulbricht Silk Road
The infamous Silk Road founder got busted because he reused usernames. He promoted his marketplace as "altoid" then later used the same handle to ask for IT help, dropping his personal email (rossulbricht@gmail.com). He also asked coding questions about Tor on Stack Overflow under his real name then changed it to "frosty" - but not before it was archived. Simple Google searches connected all these dots. Game over.
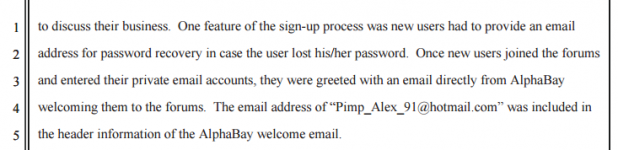
Email Addresses
Your email is basically your online SSN. Even your "anonymous" ProtonMail can fuck you if you reuse it. Remember AlphaBays welcome email? The admin included his personal Hotmail—"Pimp_Alex_91@hotmail.com"—right in the header. Game over, dumbass.
Real-World Fuckup: Alexandre Cazes AlphaBay
AlphaBay was the biggest darknet market after Silk Road until founder Alexandre Cazes made a rookie mistake. This idiot embedded his personal email - "Pimp_Alex_91@hotmail.com" - in AlphaBay's welcome email headers. The email contained his nickname and birth year, and hed used it on legitimate forums with his real name. Investigators quickly linked it to his front companies and found him living lavishly in Bangkok. They caught him with his laptop unlocked - game over.
For carders that special "anonymous" email you use to register for carding forums is an immediate liability. When that forum inevitably gets breached, that email becomes a unique identifier researchers will track across every other leaked database.
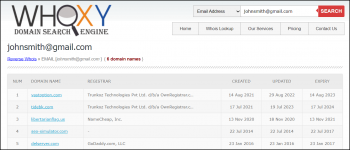
Domain Registration
WHOIS records are the gift that keeps on giving to investigators. Historical WHOIS services like DomainTools save every detail forever. One slip-up—using your real phone or email on a shady domain—and you're cooked.
Many carders set up drop shipping sites or phishing domains without properly anonymizing registration details. That phone number you used once for a domain in 2019? Its forever linked to your identity.
Writing Style
Your writing style is as unique as your fingerprint. Use "u" instead of "you"? Always forget to capitalize sentences? Have a particular way of structuring arguments? Investigators use natural language processing to match your writing across platforms. Your quirks become your handcuffs.
The way you talk in private Telegram groups is compared to your posts on public forums. That unique slang you use on carding sites? If it shows up in your Twitter replies you've just connected your personas.
Real-World Fuckup: The "Desorden/ALTDOS" Hacker
A Singaporean hacker thought he was clever by switching between aliases like "ALTDOS," "Desorden" "GHOSTR," and "Omid16B" while extorting Asian companies. His fatal mistake? His writing style remained identical across all personas. Security researchers analyzed his vocabulary and formatting patterns in ransom notes and forum posts. Despite changing names his linguistic fingerprint led investigators straight to a 39-year-old named Chia in Bangkok.
Passwords
Passwords might seem trivial, but theyre more personal and unique than your fucking fingerprints. Your password is probably something deeply personal like your dog's name mashed up with your birth year and some random-ass special characters. When you reuse that same password across multiple sites, youve created a digital DNA sample.

When some site you used inevitably gets breached and your hashed password leaks investigators don't even need to crack it. They just cross-reference that hash with other breaches. Since your password is unique enough that very few people share it, its like a neon sign pointing straight back to your real identity. Game fucking over.
Real-World Fuckup: Roman Seleznev "Track2"
Russian carding kingpin Roman Seleznev (aka "Track2") got busted through simple password reuse. Despite his technical prowess, he recycled the same passwords across both personal and criminal accounts. When feds nabbed him in the Maldives they tried a password they'd discovered from his other accounts - first try access to 1.7 million stolen credit cards. All his sophisticated hacking skills meant nothing because he couldnt be bothered with different passwords. Now he's serving 27 years.
What To Do
Now that you understand how fucked you already might be, heres how to unfuck your situation—or at least prevent further damage.

Digital compartmentalization isn't optional—its your oxygen mask in this environment. Think of each identity as a completely separate person with no connection to your other personas.
- Use dedicated devices. Your carding activities should happen on a separate machine than your personal life—preferably a Linux system booted from a USB that you only use with Tor.
- For every new forum marketplace, or community create an entirely new identity. New username, new email address (preferably through a privacy-focused service with no phone verification) and even a new writing style.
- Use a password manager like KeePassXC that stays offline. Generate unique 20+ character passwords for every single site. Store this database on an encrypted USB that never connects to networked computers.
- Check yourself before you wreck yourself. Regularly investigate your own OPSEC by searching your handles across breach databases and search engines.
- Develop healthy paranoia. Before every action online, ask yourself: "If this site gets hacked tomorrow what could this reveal about me?" Treat every interaction as potentially permanent evidence.
Conclusion
Your identity isn't revealed by some dramatic hack or high-tech surveillance. It unravels thread by thread through the mistakes youve already made and continue making every day. The web never forgets, and investigators don't need warrants or specialized tools—they just need your patterns and enough time to connect them.
The most dangerous security vulnerability isnt your VPN or your cryptocurrency handling. It's between your ears—your habits your laziness, your complacency. Master the discipline of identity isolation and you might just survive. Fail, and join the long list of cautionary tales who thought they were too clever to get caught.
In this game, youre not anonymous until proven guilty. You're connected until proven isolated. The choice is yours: develop rigorous digital discipline or eventually wear handcuffs. Theres no middle ground. d0ctrine out.