Fixxx
Moder
- Joined
- 20.08.24
- Messages
- 1,095
- Reaction score
- 4,209
- Points
- 113
A new info-stealing malware named Infinity Stealer is targeting macOS systems with a Python payload packaged as an executable using the open-source Nuitka compiler. The attack uses the ClickFix technique, presenting a fake CAPTCHA that mimics Cloudflare’s human verification check to trick users into executing malicious code. Researchers at Malwarebytes say this is the first documented macOS campaign combining ClickFix delivery with a Python-based infostealer compiled using Nuitka. Because Nuitka produces a native binary by compiling the Python script into C code, the resulting executable is more resistant to static analysis. Compared to PyInstaller, which bundles Python with bytecode, it’s more evasive because it produces a real native binary with no obvious bytecode layer, making reverse engineering much harder.
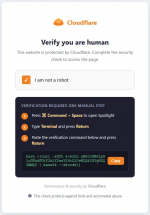
The attack begins with a ClickFix lure on the domain update-check[.]com, posing as a human verification step from Cloudflare and asking the user to complete the challenge by pasting a base64-obfuscated curl command into the macOS Terminal, bypassing OS-level defenses.
The command decodes a Bash script that writes the stage-2 (Nuitka loader) to /tmp, then removes the quarantine flag, and executes it via ‘nohup.’ Finally, it passes the command-and-control (C2) and token via environment variables and then deletes itself and closes the Terminal window. The Nuitka loader is an 8.6 MB Mach-O binary that contains a 35MB zstd-compressed archive, containing the stage-3 (UpdateHelper.bin), which is the Infinity Stealer malware.
Before starting to collect sensitive data, the malware performs anti-analysis checks to determine whether it is running in a virtualized/sandboxed environment. Malwarebytes’ analysis of the Python 3.11 payload uncovered that the info-stealer can take screenshots and harvest the following data
“The final payload is written in Python and compiled with Nuitka, producing a native macOS binary. That makes it harder to analyze and detect than typical Python-based malware,” Malwarebystes says.
Attack chain
The attack begins with a ClickFix lure on the domain update-check[.]com, posing as a human verification step from Cloudflare and asking the user to complete the challenge by pasting a base64-obfuscated curl command into the macOS Terminal, bypassing OS-level defenses.
*ClickFix step used in Infinity attacks.
The command decodes a Bash script that writes the stage-2 (Nuitka loader) to /tmp, then removes the quarantine flag, and executes it via ‘nohup.’ Finally, it passes the command-and-control (C2) and token via environment variables and then deletes itself and closes the Terminal window. The Nuitka loader is an 8.6 MB Mach-O binary that contains a 35MB zstd-compressed archive, containing the stage-3 (UpdateHelper.bin), which is the Infinity Stealer malware.
*the malware's disassembly view.
Before starting to collect sensitive data, the malware performs anti-analysis checks to determine whether it is running in a virtualized/sandboxed environment. Malwarebytes’ analysis of the Python 3.11 payload uncovered that the info-stealer can take screenshots and harvest the following data
- Credentials from Chromium‑based browsers and Firefox
- macOS Keychain entries
- Cryptocurrency wallets
- Plaintext secrets in developer files, such as .env